Within the branches of computing we find Computer Security, which is what tries to protect computer systems. As a counterpart to it is Ethical Hacking, which is the branch in charge of testing the mechanisms established by Computer Security, giving way to a new category of user, called hacker.
There are many definitions of the term “Hacker”, but in a few words we can summarize it as follows: “A hacker is a person with advanced knowledge in computing, security, networks, programming, etc. who is capable of going further than ordinary people, finding vulnerabilities and flaws in the security of computer systems. “His personal motivation may be monetary remuneration, a protest (hacktivism) or simply the challenge.”
There are several classifications of hackers, and an Underground culture has developed around them.
Hacker Ratings:
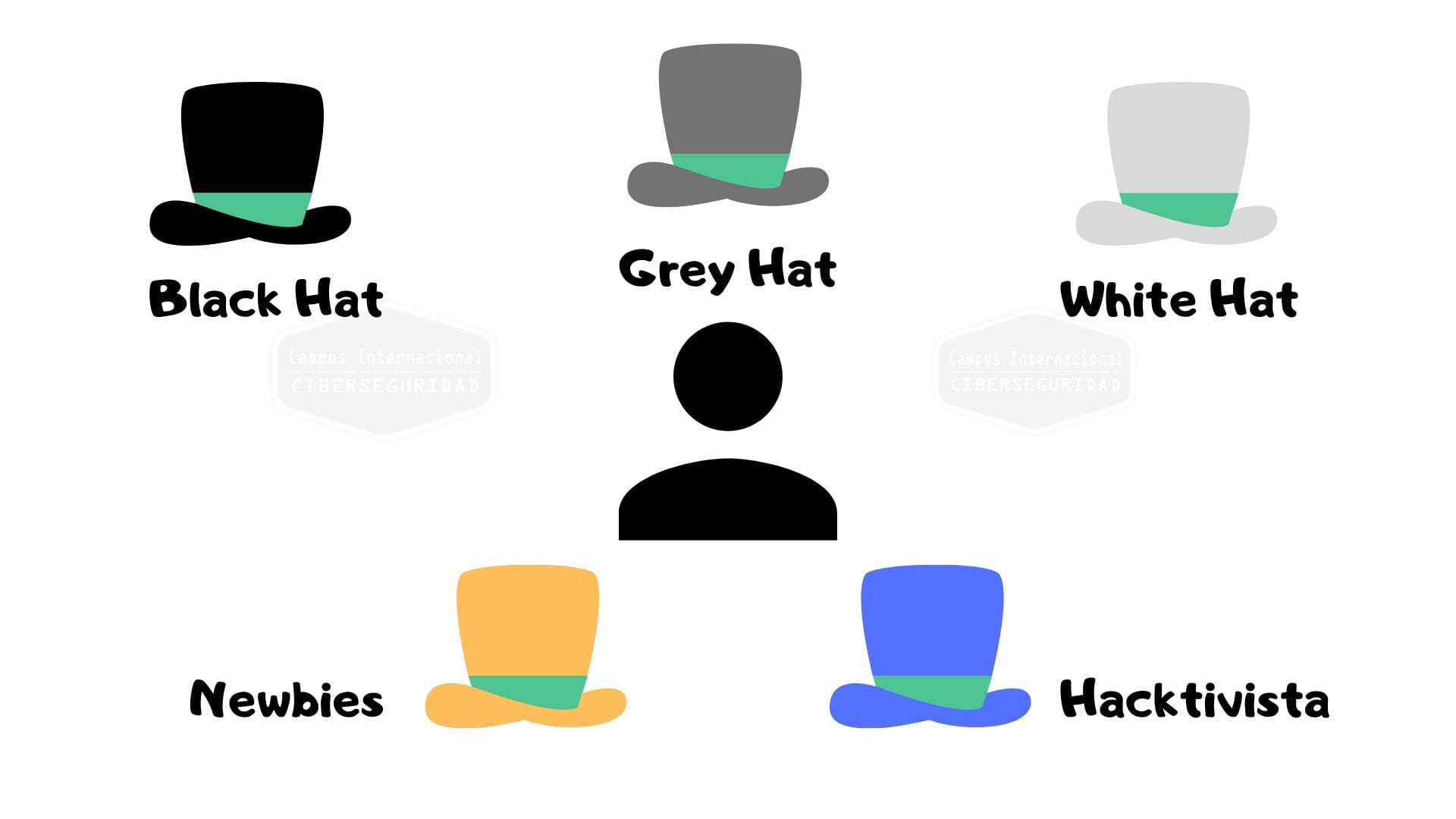
Newbie or Neophyte
It is the hacker apprentice who still does not have knowledge or experience about how technology and hacking work, but if he persists, he will surpass himself until he becomes a hacker.
Script kiddie (Niño con script)
Script (script file) kiddie ( ‘ child’, Person with little or no experience and immature). This is an inexperienced user pretending to be a hacker who breaks into systems using tools developed by others, without the mere knowledge of what it means to be a hacker.
White Hat (White Hat Hackers)
They are called Ethical Hackers. This type of hacker is well-intentioned and is hired by companies to search for security vulnerabilities in their systems or products. They generally work in computer security or antivirus consulting companies, this is what is called a professional hacker, since their profession is to be a hacker following the ethics that their work requires.
Gray Hat (Gray Hat Hackers).
This type of hacker is well-intentioned, and they practice hacking without bad intentions. He’s kind of a cyberspace cowboy. Although in his actions he performs illegal actions, they typically discover vulnerabilities in systems and products and notify their creators so that the errors can be corrected and sometimes even offer to help correct them, they are motivated by their curiosity and personal satisfaction.
Black Hat (Black Hat Hackers)
Unethical hackers. This type of hacker is ill-intentioned and motivated by personal gain. Their activity in many places in the world is considered illegal, and they are also called hackers. They are also dedicated to creating viruses, malware, exploiting servers and systems, remotely hijacking computers, networks, or information through the use of ransomware (cryptographic virus that encrypts information and demands a ransom). He infiltrates networks for the simple fact that he can. These are the bad boys of cyberspace, and they are also often called Cracker.
Hackative
It is the one that uses hacking to proclaim a social, ideological, religious or political message. Generally, hacktivism activity involves the defacement of sites or denial of service (DDOS) attacks. Examples of this type are Anonymous, which is a group well known for its critical position towards Scientology.
Myths vs. Reality
Movies and series deceive us about hackers. In most scenes in which hackers are referenced, they can practically perform feats, magic, so to speak. The protagonists can identify viruses in systems, analyze large volumes of data, bypass firewalls, program complex routines and even etc. Just by typing meaningless things, and in a few seconds they have already hacked the CIA, the NSA, the Pentagon and even accessed any system. In real life, access to a single system can take up to months of intense work in various ways.
The procedure of a hacker in general follows the following steps
1-Definition of an objective (What system or systems are going to attack)
2-Reconnaissance or Exploration (Exhaustive compilation of all the information they find, public or not)
3- Attack (Explotation)
4-Escalating privileges (having maximum permissions on the compromised system)
5-Maintaining access (Installing back doors for possible future access) (Backdors, rookits)
6- Cleaning traces (Deletion of traces, logs and all possible logs of the systems to try to hide their access)
In subsequent articles, more will be discussed this topic and many others related to computing in all its branches.